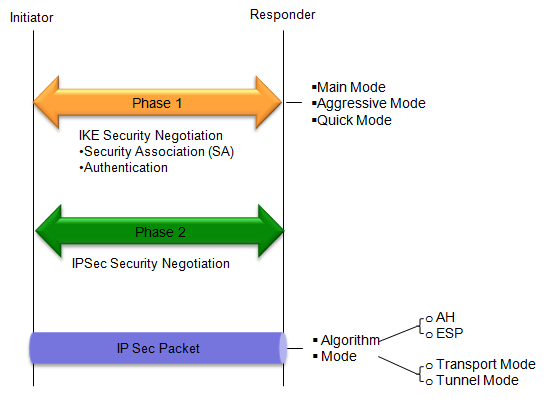
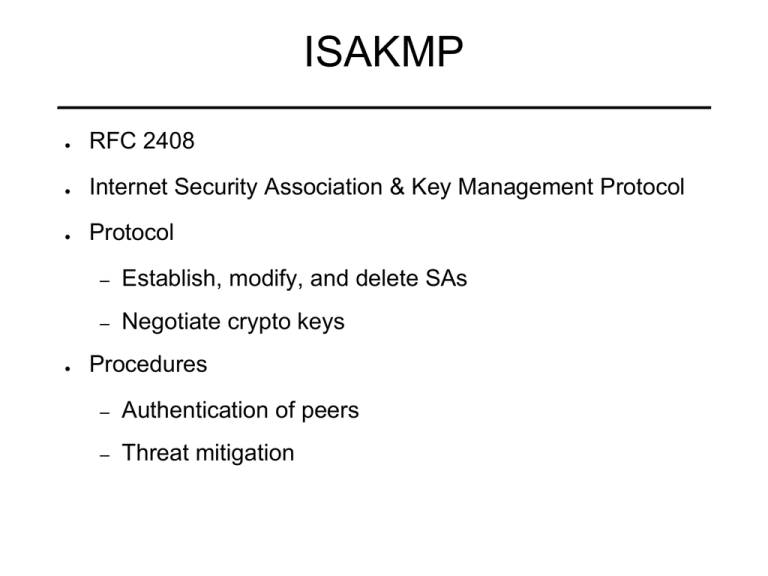
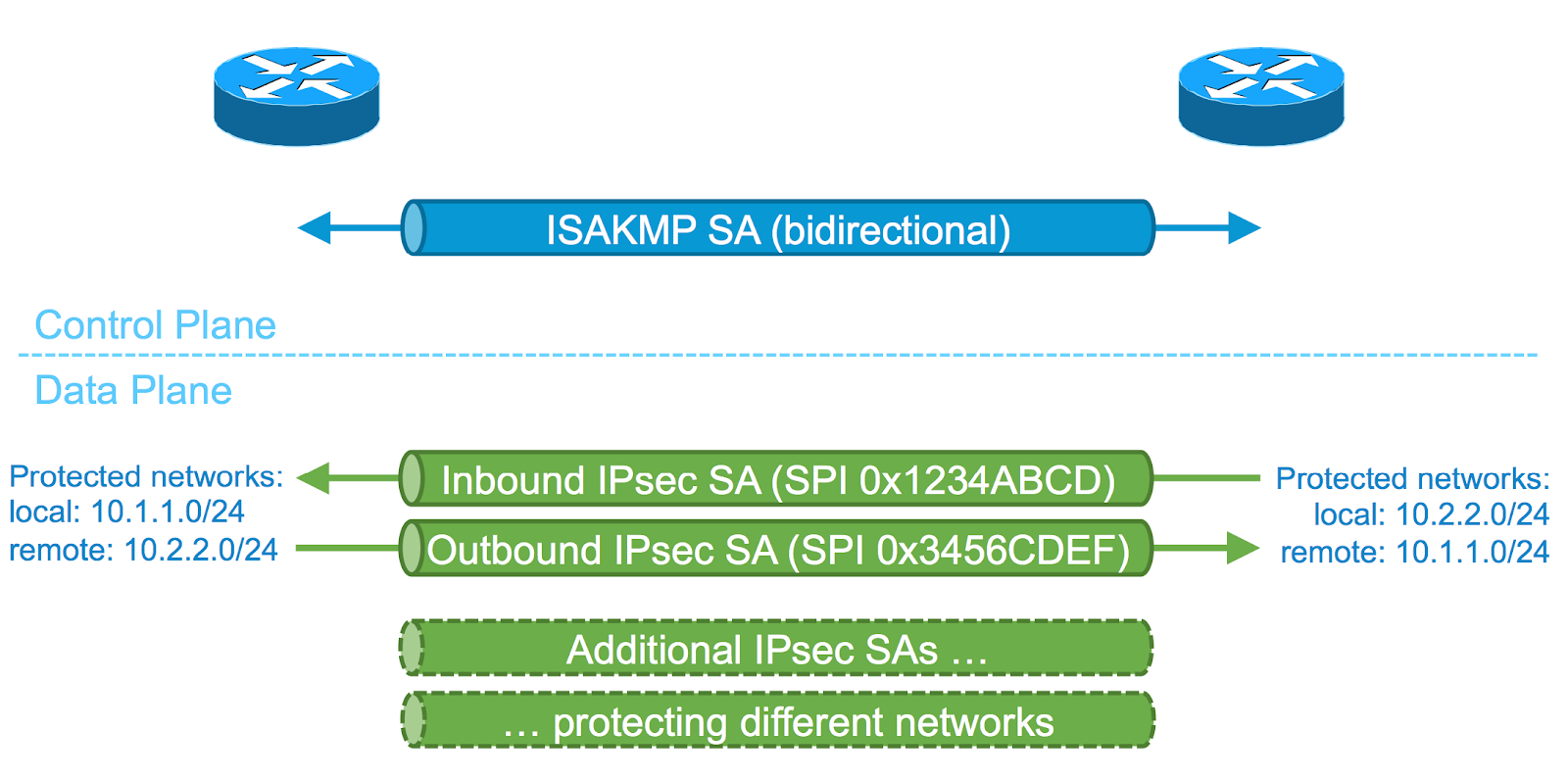
Internet Key Exchange (IKE) and Security Association (SA) by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

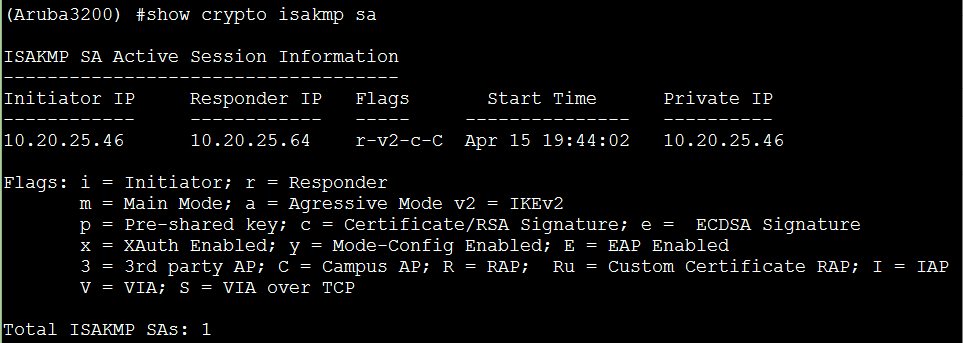
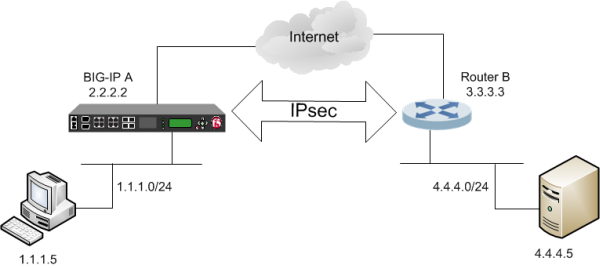
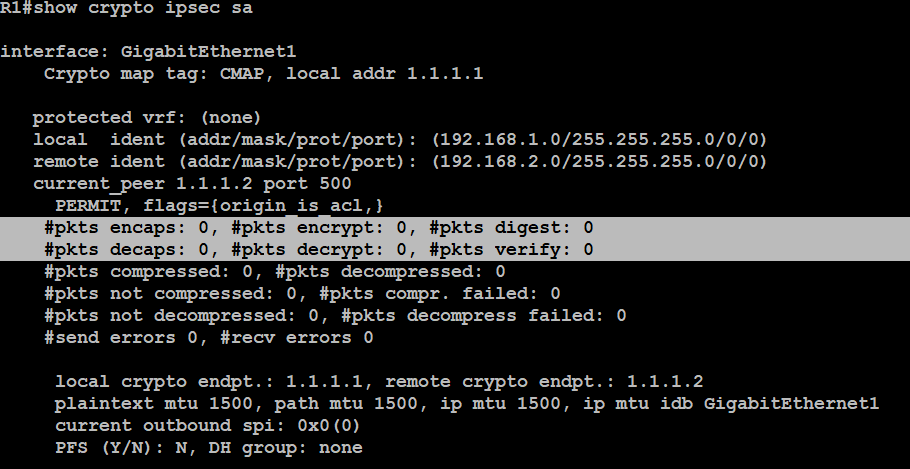
Configuring site to site IPsec VPN tunnel between F5 LTM and Fortinet Fortigate | Richard Lara's Blog
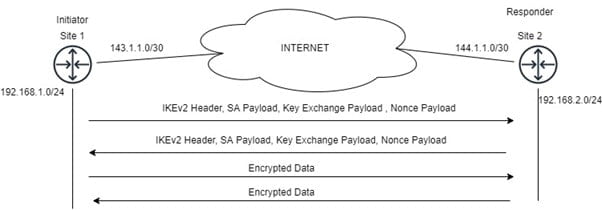
How does IPsec work with IKEv2 and establish a secure tunnel between two sites? | Zindagi Technologies